Nobody sets out to build a mess. Every fintech CTO who has assembled a lending stack from five different vendors did it with perfectly reasonable intentions. They picked the best loan origination system on the market. They chose the most respected AML compliance provider. They selected a payments processor with solid API documentation. Each individual decision made sense.
And then they spent the next 14 months debugging why none of them talk to each other properly.
This is the story of the fintech lending stack — how it gets built, why the costs stay hidden until they are absolutely not, and what the people who have been inside those environments have learned about what actually happens when you assemble critical financial infrastructure from parts.
The Plan Always Looks Reasonable on a Whiteboard
Picture it. You are in a product planning session. Someone has drawn a clean architecture diagram on a whiteboard. Box A is the loan origination system. Box B is the servicing platform. Box C is KYC. Box D is the AML engine. Box E is the payments processor. Each box has a name — a vendor you have evaluated, a trial account you have created, a sales call where everything sounded straightforward.
Between each box is a thin line. On the whiteboard, those lines look identical. In reality, each one represents weeks of integration work, version compatibility testing, error handling across systems that do not share a data model, and eventually a dedicated Slack channel called something like #vendor-api-issues that everyone has muted.
The whiteboard is lying to you. Not maliciously. It just cannot show you what happens in those lines.
The visible cost of a multi-vendor fintech lending stack is the licence fees. The invisible cost is everything that happens between the boxes on the whiteboard.
What the Integration Tax Actually Looks Like
Let us be specific, because the lending industry has a habit of speaking vaguely about ‘integration overhead’ in the same way people talk vaguely about ‘technical debt’ — as something that is generally understood to be bad but rarely quantified until someone is sitting in a board meeting explaining why the go-live date has moved again.
Here is a realistic timeline for a fintech team building a US lending product from a five-vendor stack. These numbers are drawn from patterns observed across real deployments, not invented for effect.
Month 1–2
Vendor selection and contracts
Month 3–4
API documentation review and scoping
Month 5–7
The build begins — and slows down
Month 8–10
The vendor update problem
Month 11–14
Testing, compliance review, and the delayed launch
Month 1–2: Vendor selection and contracts
This part feels productive. You are evaluating platforms, reading documentation, sitting on demos. You pick your five vendors. You negotiate contracts. Four of the five have different billing cycles, different SLA structures, and different data retention policies that your legal team will want to review. You spend two weeks getting contracts aligned enough to sign. Nobody counts this as integration time, but it is.
Month 3–4: API documentation review and scoping
Your engineering team starts reading the actual API documentation. Not the marketing pages — the real docs. This is where the first gaps appear. The loan origination system’s webhook structure does not map cleanly to the way the servicing platform expects to receive event data. The AML engine requires a customer identifier format that the KYC provider does not output by default. These are not dealbreakers. They are just the first signs that those thin lines on the whiteboard are going to require code.
Scoping estimate from your lead engineer: 800 to 1,200 hours of integration work. You nod and say that seems reasonable. It is not.
Month 5–7: The build begins — and slows down
Integration development starts. The first two weeks go well because everyone is working on the easy parts — basic API connectivity, test environment setup, initial data flows. Then someone discovers that Vendor C’s sandbox environment does not behave the same way as their production environment. Three weeks are spent debugging behaviour that will never occur in production. The schedule slips by three weeks.
Concurrently, your compliance team has started reviewing the data sharing agreements between your AML provider and your KYC provider. It turns out they cannot share certain customer data directly — it has to be routed through your own systems first. This changes the integration architecture. The lead engineer updates the estimate. It is now 1,400 to 1,800 hours.
Month 8–10: The vendor update problem
This is the moment nobody warns you about in the sales process. One of your five vendors releases a major platform update. Their API version 2.4 is being deprecated. Version 3.0 introduces breaking changes in three endpoints that your integration depends on. You have 60 days to migrate.
You migrate. It takes six weeks. During those six weeks, two other vendors release minor updates that require testing. Your team has not started building the actual product features yet. They are maintaining the infrastructure that is supposed to allow them to build product features.
Month 11–14: Testing, compliance review, and the delayed launch
End-to-end testing begins. This is where the multi-vendor architecture reveals its most expensive characteristic: when something goes wrong, nobody owns it. The loan origination system says the data left their platform correctly. The AML engine says the data arrived in an unexpected format. The servicing platform says it cannot process the event because the timestamp format from the payments processor is non-standard. Every support escalation bounces between three vendor queues before someone figures out that the problem is in the translation layer between two systems — which is code your team wrote, which means nobody else’s SLA covers it.
Launch is pushed from Q2 to Q3. Then Q3 to Q4. Your investors ask why. You explain ‘integration complexity.’ They nod and write it down.
The Numbers Nobody Puts in the Business Case
Here is what a multi-vendor fintech lending stack costs beyond the licence fees. These are conservative estimates based on mid-market engineering costs in the US market.
|
Cost category |
Estimate |
Often ignored? |
|
Initial integration engineering |
800–1,800 hours |
No — always in budget |
|
Annual API maintenance (per vendor) |
150–300 hrs/year × 5 vendors |
Almost always |
|
Delayed go-live (revenue not earned) |
3–6 months × monthly run rate |
Always |
|
Multi-vendor support overhead |
4–8 hrs/week of engineering time |
Always |
|
Compliance data reconciliation |
2–4 hrs/week of compliance time |
Always |
|
Re-architecture when a vendor pivots |
400–800 hours, happens every 18–24 months |
Always |
Add up the ongoing items — API maintenance, support overhead, and compliance reconciliation — and you are looking at 900 to 1,500 engineering hours per year spent maintaining a fintech lending stack that is not getting better. It is just staying operational.
That is time your team is not spending on product differentiation, on new loan products, on improving the borrower experience, or on any of the things that actually create competitive advantage in the lending market.
The Audit Trail Problem — The One That Stings the Most
Here is a scenario. A regulator contacts you. They want an audit trail for a specific loan — origination through final repayment. Complete. They want it in two weeks.
In a single-platform architecture, this is a database query. Maybe two. You have the answer in an afternoon.
In a five-vendor stack, this is a project. You pull the origination record from Vendor A’s export API. You pull the KYC verification record from Vendor C’s dashboard. You pull the AML screening log from Vendor D’s case management system. You pull the disbursement and repayment records from the payments processor. You pull the servicing events from Vendor B’s reporting module. You reconcile the timestamps — which, inevitably, are in three different time zones and two different formats. You cross-reference the customer identifiers — which, equally inevitably, are slightly different across systems because each vendor assigned their own internal ID.
Two weeks later, you hand over a PDF that you have assembled manually from six exports and a lot of careful copy-pasting. The regulator looks at it. They ask why some of the timestamps are in UTC and some are in Eastern Time. You explain. They make a note.
This is not a hypothetical. It is a description of what compliance teams in multi-vendor lending operations deal with every time a regulator asks for anything.
When a regulator asks for an audit trail and gets a CSV export from four different systems, that is not a compliance failure. It is an architecture failure dressed up as a compliance process.
What 'Native' Looks Like in Practice
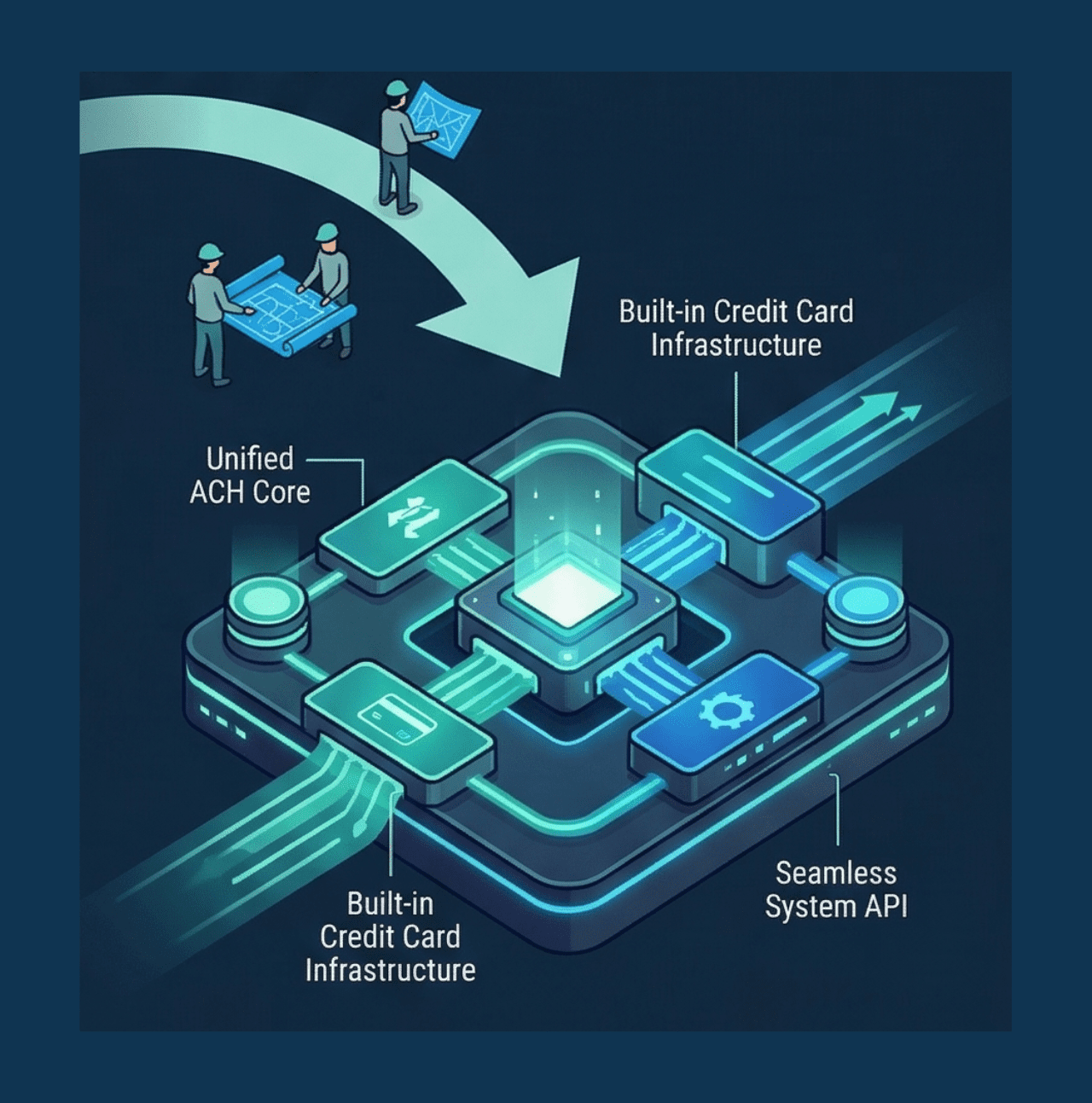
The alternative to the five-vendor assembly is a platform where all six layers — lending, AML, payments, core banking, cards, and security — are built natively in the same codebase, sharing one data model, deployed as one system.
In that architecture, the audit trail question takes an afternoon. Because there is only one system to query. The AML check for a loan application runs in the same transaction as the origination event — not in a separate system that is called via API three seconds later. A disbursement updates the core banking ledger in real time — not after a sync that runs every fifteen minutes. A regulator request for a complete loan record returns a complete loan record, because it was always one record.
The go-live timeline for a native platform deployment is 6–8 weeks. For the full stack. Not for a single module — for all active layers, configured to your product specification, deployed and tested.
That is not a marketing claim. It is what happens when you remove integration work from the critical path.
The Question Worth Asking Before the Next Contract
If you are currently in the process of evaluating vendors for a lending product build, or if you are twelve months into a multi-vendor integration and wondering how you got here, the question worth asking is not ‘which vendor has the best feature set?’ It is ‘how much of my engineering capacity will be spent on maintaining the connections between vendors rather than building the product?’
There is a version of fintech infrastructure where that question has a clean answer: none of it. Because the connections do not exist. The layers are native.
That version exists. It just requires choosing the right architecture before the whiteboard gets complicated.
The Bottom Line
The five-vendor fintech lending stack is not a bad idea that only bad engineers pursue. It is what the market has offered for the last decade. The alternatives have historically been ‘build it yourself’ (expensive, slow, and you end up with five internal teams doing the same integration work) or ‘use a managed BaaS provider’ (fast to start, expensive to scale, and you never fully own the stack).
A third option — a natively built full-stack fintech infrastructure platform — is a newer entrant. But it is the one that eliminates the integration tax from the start. Not by simplifying the problem. By removing it from the equation entirely.
Because the line between two systems on a whiteboard is only thin until someone has to write the code that lives in it.